Remote Control
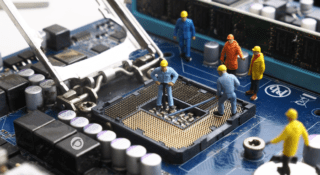
How to update your PC BIOS
Content: Introduction Accessing the BIOS from Windows Alternatives to using the Windows 10 and 11 method What does UEFI stand for? When should you update your BIOS? How to update your BIOS BIOS Update Considerations Every computer has its BIOS, short for Basic...
How to reduce CPU usage
From the computer, we increasingly perform different tasks simultaneously (listening to music while writing a report, receiving files by email and downloading videos), which involve executing commands, and sending and receiving data. Over time,...
AR vs VR: What’s the difference?
It would seem like the line between science fiction and reality is increasingly blurred. We no longer see this only in the movies and games, but in e-commerce, education, entertainment, staff training, remote diagnostics or architectural...
What is RMM software?
In this article, we will thoroughly address RMM Software (Remote Monitoring and Management Software) and its essential role for Managed Service Providers (MSPs). We will explain the core functions of RMM, from remote monitoring to efficient...
Unraveling the Dangers of Phishing: From Basics to Effective Prevention
Surely you may have at one time or another received an email warning of an outstanding invoice, a parcel shipment that you did not expect or a warning from the bank about suspicious activity in your account. These messages usually adopt an...
What is remote access? An open door to productivity and flexibility
What is remote access and how has it transformed work dynamics around the world? Let's dive in, explore and discover together how this innovative practice has reshaped conventional work structures and opened up a whole range of possibilities!...
What is RAM memory? How does it affect your computer?
There is basic knowledge, like freshman year computing, which we often take for granted but that is always a pleasure to remember. From how to take a screenshot to where to find stickers thick enough to blind a laptop's webcam, to...
What is websocket? That’s the question
Many of you will have heard about this new component in HTML5, but, even so, you don't understand how to work with websockets. Content: What is websocket? Computer-to-Computer Dialog If I've seen you I don't remember What is websocket, then? Do...
Centralized management in your company: save time and space
"Pragmatism", "saving" and "effectiveness" are words that should be engraved on your brain, especially if you are one of those who want their business to be profitable. But let us add a new one right now: “centralized management”. There are many...
¿HDD or SDD?
HDD or SDD? This is a question that just a few of us considered a couple of years ago. However, lately, the storage unit battle has borne witness to what has become a tough competition. Do you have no idea what the differences between both types...
Let’s find out all about secure remote access software
We live in a very modern age, a time of conspiracy myths and legends, where today's computer trolls and malwares are mean and cruel, and users are attacked with all kinds of suffering. These days only one blog about technology dared to challenge...
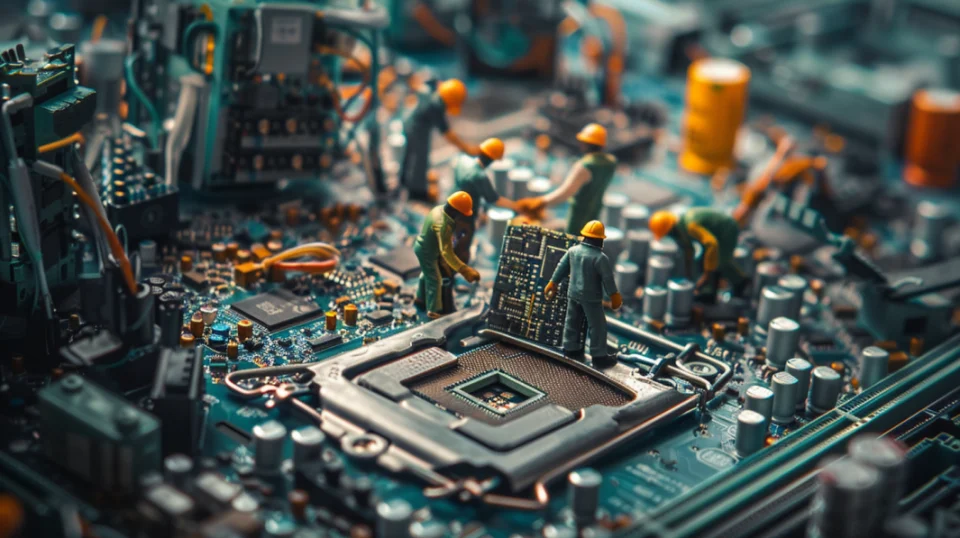
3 levels of systems maintenance
The systems maintenance is an activity that is becoming more and more important. Many companies, which increasingly depend on Information Technologies, have realized that a correct investment in maintenance can mean savings in the medium and...
8 ideas for preventive maintenance for computers
Oh boy, those computers! We can use them for many things ... For leisure, for work, for social relationships, for watching videos on YouTube, yeah they are quite useful. If you have ever used a computer, you will know that you have to take care...
8 advantages of digitalization of business
Di-gi-ta-li-za-tion. That word thrills some people and frightens others equally. Let's talk a little bit about it. If you have a business, multiple digitalization options may have already occurred to you. And even if you know that a digital...
The role of a system administrator
Are you a System Administrator? Do you need to hire one? Well, this is quite common! It is one of the most popular job positions out there right now. If we had to think about one job position with a massive boom in the last years, then this...
The profile of a Technical support analyst
The position of the technical support analyst is an emergent work position. Information technologies encompass everything and nowadays more companies provide services in which information technology is essential. In addition to this, new...
Computer overheating. What can I do in order to avoid this?
When summer arrives... the temperature of your laptop gets quite warm, so you go mental and you start to panic. Well, you are not the only one! One of the qualities of laptops is that they tend to overheat more often than computers; this is...
4 types of IT maintenance
Do the computers in your office roar like lions and burn like embers in the underworld? Have your computers taken over the kitchen? Have your computers spent the morning drinking coffee and playing darts? What did you expect? Just like any other...
Advantages of remote computer support
In the antediluvian period, the Internet did not exist. We know right, can you imagine a world without Internet? Imagine a world without social networks or email. Imagine that you have a problem on your computer but you’re not able to solve it...
6 ideas to organize your desktop
Have you seen the horrible look of the desktop of your computer? The shortcut icons to the work software are mixed with the photos of your last holiday in Ibiza and videos of funny cats. And then you find yourself complaining about those files...
Computer technical support for companies: a pretty good idea
Do you own a company or do you work in one? Have your computers started doing weird things? Have they lined up and begun to dance the conga? If this is what you are witnessing, then you might be suffering from hallucinations, so you should visit...